Mike VanDelinder, a product manager at Jamf for Jamf Connect, and Joel Rennich, Jamf Connect's director, ran attendees through developments in Jamf Connect passwordless authentication and offered a demo of the latest iteration.
What about this flow makes it passwordless?
Jamf Connect's mac identity management allows for an integration between an organization's cloud identity provider and user accounts, synced passwords, etc. One individual can set up and use the same username and passwords for all of their services. It's basically using a credential derived from your IdP to access your Mac using your phone.
Jamf Connect developers have created an app for the iPhone that can use credentials to log into a nearby Mac using Connect. Connect behaves like a smartcard: cards or security keys used for computers or networks.
And it's very secure:
- Certificate stored on phone
- Protected by secure enclave
- Requires biometrics to use
- Cannot be exported from phone
- Follows existing certificate security process
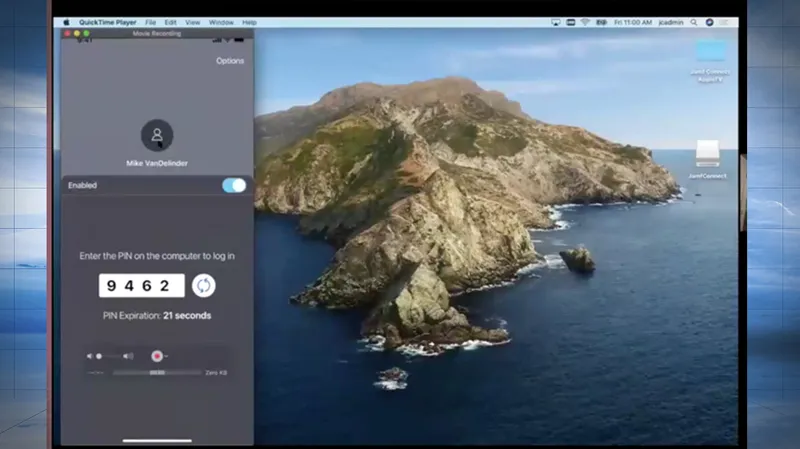
After a user accesses their iPhone, they can then log into their account or enter a PIN. They don't need extra hardware. Just an iPhone and Mac to sign into accounts.
- Users can have multiple devices associated with their accounts
- User accounts can still have a password associated with them if that extra layer is what they'd like.
The point of this app: it's meant to be a convenience, not a security bypass.
Passwordless Tech Overview
Here's what tech the app uses:
Crypto TokenKit: the iPhone appears as a smart card to macOS. It can sign, decrypt, and exchange keys just like any smart card without any physical contact needed.
PKI: Sign-in operations and authentication are already built-in on the Mac.
Multipeer Connectivity: This uses WiFi (infrastructure and adhoc) to connect Mac to an iPhone, and is double-encrypted: both via Multipeer Connectivity and Jamf Connect. Belt and suspenders! There is no configuration required for the connection to work.
Passwordless Tech: we use CoreBluetooth when the iPhone is locked--the Mac acts as a Bluetooth beacon to wake the phone and show notification on the lock screen. We also use it as a possible fallback if WiFi is disabled.
Setup
iPhone Setup
- Deploy Jamf Connect from the App Store
- Authenticate to a cloud identify provider
- Get a certificate from Microsoft NDES, based on your cloud identity service (Any IdP that supports OpenID Connect flows should work).
- Continue using sign in on the phone via Face ID or Touch ID. The gates all of these interactions.
Mac Setup
Install the Jamf Connect package and scope with config profile.
Enrollment Flow
- Set up Connect on an iPhone
- Enroll Mac with customized enrollment authentication
- Jamf Connect creates a new local account on the Mac matching the enrolled user's name if a phone with the same certificate can be discovered.
Secure Communications
- All communications are encrypted in addition to Bluetooth or MultiPeer Connectivity encryption
- Ephemeral keys are used for each connection between iPhone and Mac
- An optional PIN can be used as well as biometrics on the iPhone.
When you can keep your iPhone next to your Mac, do sudo, click on locks -- and authenticate just by turning your head for face ID, It's a very nice experience.
Here's how the security flow works:
- Generate ephemeral keys
- Encrypt payload with public key from iPhone
- Send payload to phone
- Decrypt payload using private key
- Encrypt response with ephemeral key
- Send response to Mac
- Decrypt with ephemeral key and process result
Mike VanDelinder and Joel Rennich demonstrated the app -- take a look at the full Passwordless authentication with Jamf Connect video to watch it yourself and to learn far more detail on the technical specifics of how this works.
Subscribe to the Jamf Blog
Have market trends, Apple updates and Jamf news delivered directly to your inbox.
To learn more about how we collect, use, disclose, transfer, and store your information, please visit our Privacy Policy.
