This past summer, we touched on the Jamf Pro and Splunk Add on in our webinar and subsequent blog, Level up your reporting capabilities with Jamf. Today, in the JNUC session, Securing a modern, distributed workforce with Jamf and the Jamf add-on for Splunk, Kevin Friel and Lisa Davies from Redox joined Jamf Nation to dive into the need for and impact of this integration.
The key goals of leveraging the Jamf Pro and Splunk integration:
- Keep the security team happy with visibility to endpoint data the way they want to see it
- See just how easy it is to create useful dashboards, reporting and alerting
- Help Security help themselves by using familiar or industry-standard tools to query the valuable data
- Leverage data and analysis to anticipate IT support needs and maintain a positive end-user experience within a distributed workforce.
This integration is key to Redox in supporting their distributed workforce while maintaining the same end-user focused experience they've always sought to provide. As an Apple shop, addressing the IT challenges that are presented with a distributed workforce who the same IT staff, regardless of location, relies on native Apple features and best practices, first and foremost.
Friel shared that, when asking what changes in this process due to a distributed workforce, it was clear that "the role of managing devices and supporting end users is basically the same, but how we go about doing it has to be quite different." To Redox, this meant truly embracing zero-touch deployment, managing and supporting devices with Jamf, and bringing data and information that was spread across the numerous best-in-class tools that support their operations together for security reporting and analysis.
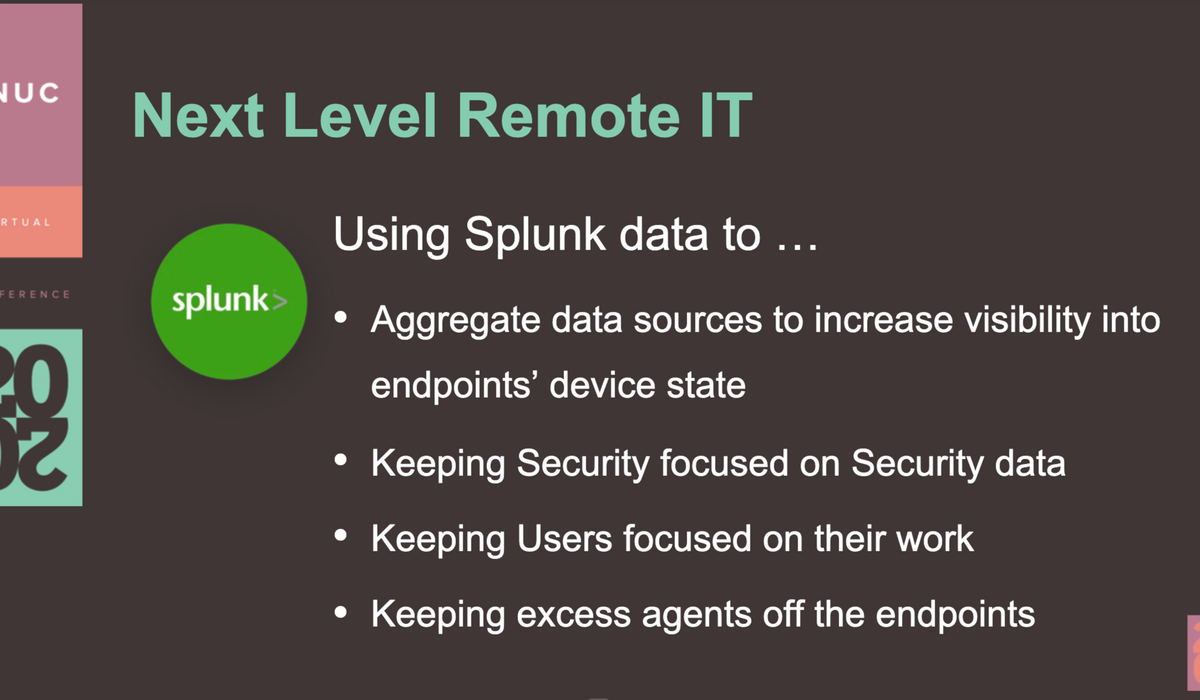
The Jamf Pro integration with Splunk empowers the Redox security team to take the extensive, reliable data provided by Jamf Pro and bring it together under one lens with the other tools for actionable insights and interactive reporting, and to discover common issues from aggregated data. The end-vision for Redox is for "next-level remote IT" meaning after system data and logs could be scanned after one user experiences an issue to identify other users with data identifying the same issue that has not yet been addressed or, even better, data trends that allow for IT to anticipate and eradicate the issue before it is experienced. Now, this is a future vision, but the steps to get to this next-level of remote IT support is to:
- Collect and report on troubleshooting data
- Identify the best way to handle local macOS logs en masse
- Create meaningful Self Service tools to keep security teams focused on security and empower users to support themselves
It was important to do this without adding additional agents to the Mac. Instead, all the data is leveraged from the carefully screened and already implemented agents.
Lisa Davies, Security Engineer at Redox, shared the steps of the integration process and the first steps into putting this goal into action with Jamf Pro and Splunk:
- Configure Splunk integration in Jamf Pro
- Create Splunk service account
- Create an advanced saved search
- Install Splunk Jamf Add-on in Splunk
- Create Index
- Configure the inputs
With a step-by-step walkthrough of this process, Davies demonstrated how Splunk leverages the connected data from the integration to present insights in dynamic and digestible ways like heat maps, pie charts, and customizable dashboards.
It might be intimidating to get started, but here's what you should do:
1. Find the Jamf Pro Splunk integration in the Jamf Marketplace
2. Download the Jamf Pro Add-on for Splunk
3. Watch the JNUC session on demand.
And as always, leverage Jamf Nation to learn from and collaborate with IT and security professionals.
Subscribe to the Jamf Blog
Have market trends, Apple updates and Jamf news delivered directly to your inbox.
To learn more about how we collect, use, disclose, transfer, and store your information, please visit our Privacy Policy.