Manage smarter. Secure every layer.
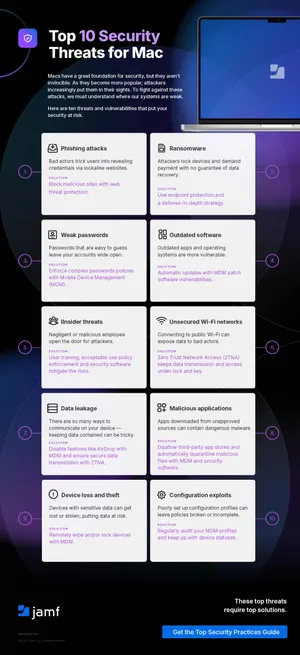
Mac adoption in business has grown by 76%, and with that growth comes new security considerations. More endpoints mean more configurations to manage, more credentials to protect and more threats to defend against.
This white paper outlines the essential security practices for building a secure, scalable Mac environment. It starts with the three foundational solutions every Mac program needs, MDM, identity and access management and endpoint security, then breaks down key practices across seven categories.
What you'll learn:
- How MDM, identity and access and endpoint security work together as the foundation for Mac management and security
- Specific practices across seven areas: device enrollment, endpoint protection, IAM, patching, threat detection, data encryption and network security
- How to enforce compliance with frameworks like SOC 2, ISO and HIPAA through automated, policy-based workflows
- Real-world outcomes from organizations using Jamf to reduce provisioning time, improve threat response and maintain compliance at scale
Download the white paper to evaluate your Mac security practices and identify where to strengthen your approach.