Simplify management. Strengthen Mac security.
As Mac adoption grows, so does the need for a security strategy that scales without adding operational complexity. Disconnected tools and manual processes create blind spots, slow response times and unnecessary overhead.
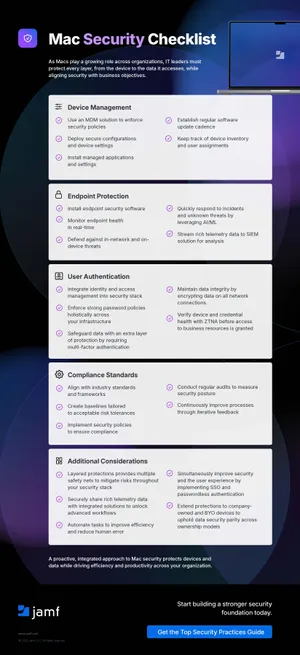
The Mac Security Checklist outlines how to bring device management, endpoint protection and identity together to reduce risk, improve visibility and support a more efficient, secure environment.
What you'll see:
- Key actions across five core areas: device management, endpoint protection, authentication, compliance and layered defense
- Specific practices such as enforcing MDM policies, requiring MFA, streaming telemetry to your SIEM and responding to threats in real time
- Additional considerations like extending protection to BYO devices, enabling SSO or passwordless authentication and automating key workflows
Download the Mac Security Checklist to strengthen your security posture and build a scalable foundation for your Mac fleet.