Last month, the third annual "Objective by the Sea" (OBTS) conference was held in Maui. As the world’s only fully dedicated Mac security conference, OBTS serves as a proponent for macOS security efforts and the larger Apple community.
Jamf talks at OBTS
Jamf employs some of the top macOS security researchers in the world, with several presenting innovative talks at OBST v3.0.
Jaron Bradely, the team lead of macOS detections at Jamf, presented "Grafting Apple Trees”.
Jaron noted that during an incident response investigation, one of the most important items you collect is a list of running processes. On most platforms, this allows you to map out a process tree using pids and ppids. However, due to Apple's unique XPC behavior, the majority of all processes end up getting created as a child of launchd which provides little value to incident response analysts.
In his talk, he presented a new method of building a process tree that actually benefits incident responders using the procinfo output — and released a free tool, "TrueTree", that implements his research.
Patrick Wardle, a principal security researcher at Jamf, presented: "Documents of Doom: Infecting macOS via Office Macros"
Patrick's talk noted that on the Windows platform, macro-based attacks embedded in documents are well understood, however on macOS they have received far less attention from the research and security community.
All the while, such attacks are growing in popularity and are quite en vogue on Macs.
He began by analyzing recent macro-based attacks that target Apple's desktop OS, highlighting macOS-specific exploit code and payloads. Rather unsurprisingly though, these attacks are unsophisticated, requiring explicit user-approval to run the malicious macro code and remain constrained by Office's constrictive sandbox.
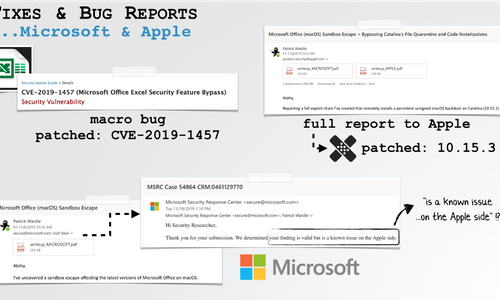
However, things could be worse! To end his talk, he detailed a novel exploit chain that started with CVE-2019-1457, leveraged a new sandbox escape and ended with a full bypass of Apple's stringent notarization requirements. Ultimately, he showed that by simply opening a malicious (macro-laced) Office document, no other user interaction required, even a fully patched macOS Catalina system could be persistently infected!
(Note: Jamf worked closely with both Microsoft and Apple to report all bugs (long) prior to the talk. And as such, all bugs have now been patched).
Jaron and Patrick both work on Jamf’s dedicated macOS security solution, Jamf Protect.
Learn more about Jamf Protect
Jamf + #OBTS's "Aloha Armory"
For the first time ever, #OBTS partnered with the renowned ToolsWatch.org to promote open-source security tools demonstrations at the conference.
As the exclusive sponsor of this event, Jamf provided both financial and
logistic support to make this event a reality and an amazing success.
During each day of the conference, independent tool developers demonstrated their open-source tools at the "Aloha Armory".
Demonstrations included:
- TrueTree (Jaron Bradley)
- APOLLO (Sarah Edwards)
- AutoMacTC (Jai Musunuri / Erik Martin)
- iOS Debugger (Brandon Azad)
Get started with Jamf Protect
Learn more about Jamf Protect
by Category:
Have market trends, Apple updates and Jamf news delivered directly to your inbox.
To learn more about how we collect, use, disclose, transfer, and store your information, please visit our Privacy Policy.